Symmetry | Free Full-Text | Privacy Amplification Strategies in Sequential Secret Key Distillation Protocols Based on Machine Learning
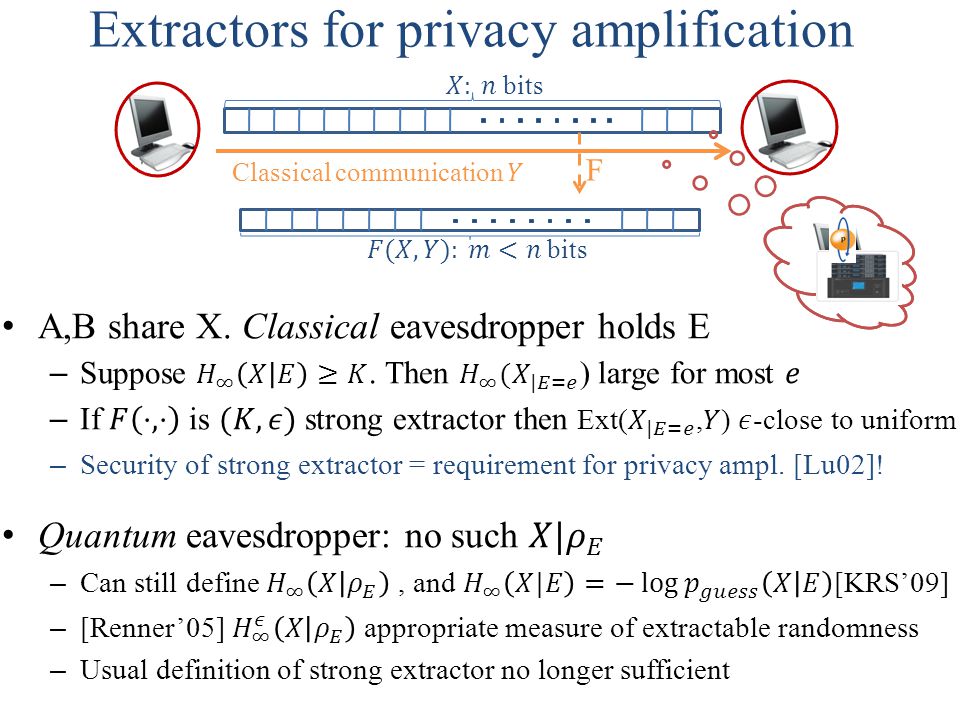
Randomness Extraction and Privacy Amplification with quantum eavesdroppers Thomas Vidick UC Berkeley Based on joint work with Christopher Portmann, Anindya. - ppt download
High-speed and Large-scale Privacy Amplification Scheme for Quantum Key Distribution | Scientific Reports
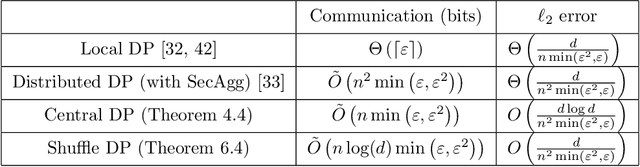
Privacy Amplification via Compression: Achieving the Optimal Privacy-Accuracy-Communication Trade-off in Distributed Mean Estimation: Paper and Code - CatalyzeX
![PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5ab3cb538f80f4bbf539103464fe597ba2d93a7c/1-Figure1-1.png)
PDF] High-Speed Privacy Amplification Scheme Using GMP in Quantum Key Distribution | Semantic Scholar

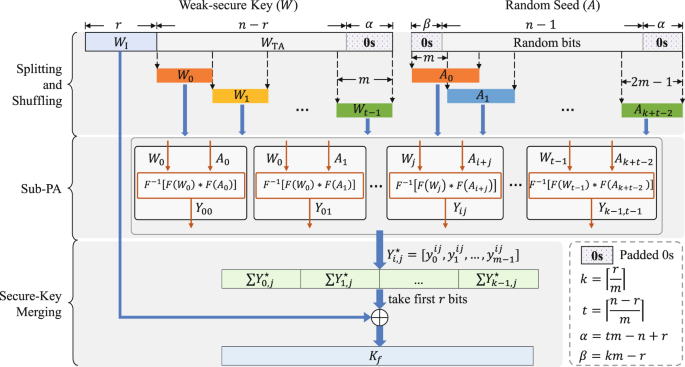
The process of length-compatible privacy amplification algorithm. The... | Download Scientific Diagram
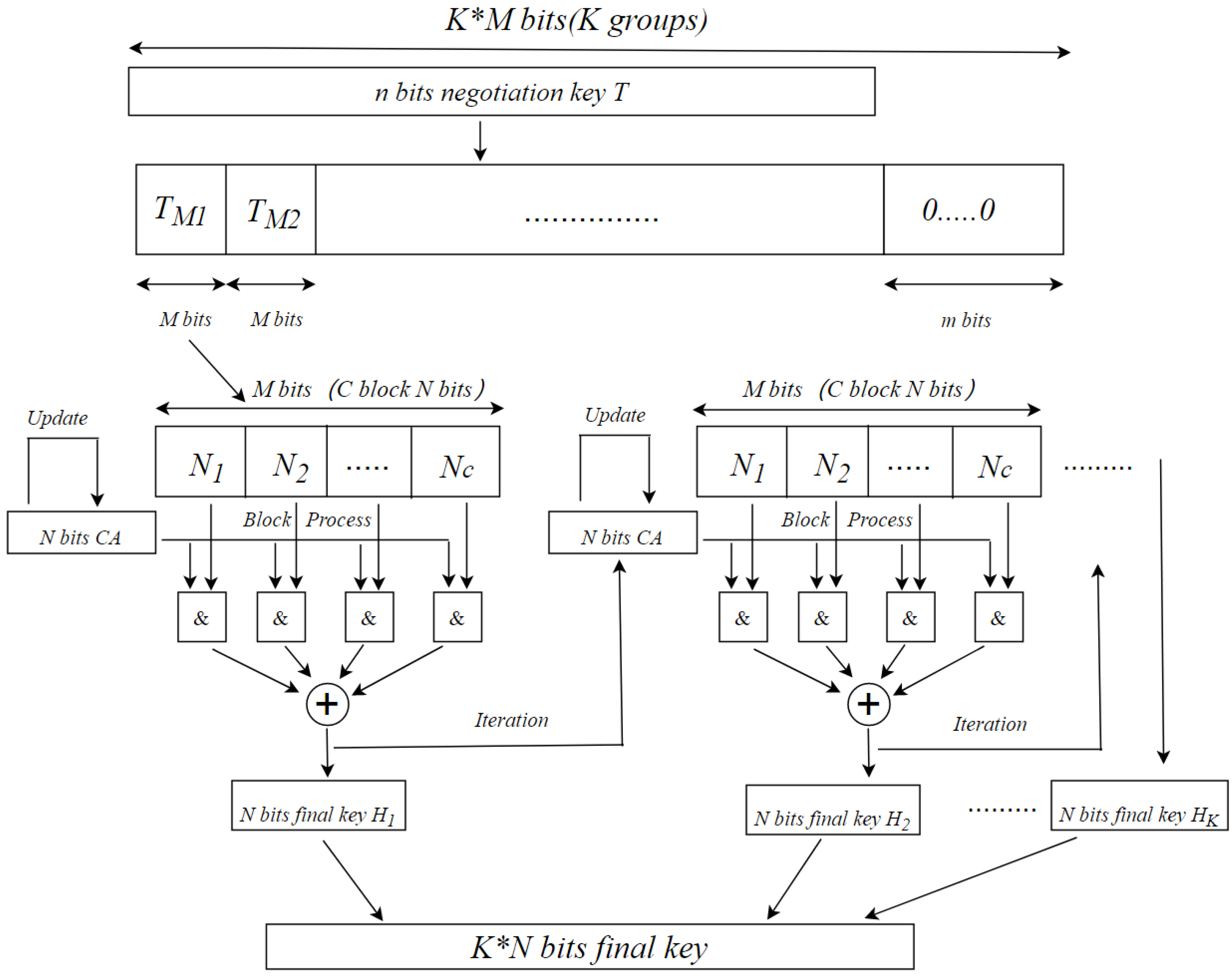
Electronics | Free Full-Text | High-Speed Privacy Amplification Algorithm Using Cellular Automate in Quantum Key Distribution

High-speed and Large-scale Privacy Amplification Scheme for Quantum Key Distribution | Scientific Reports
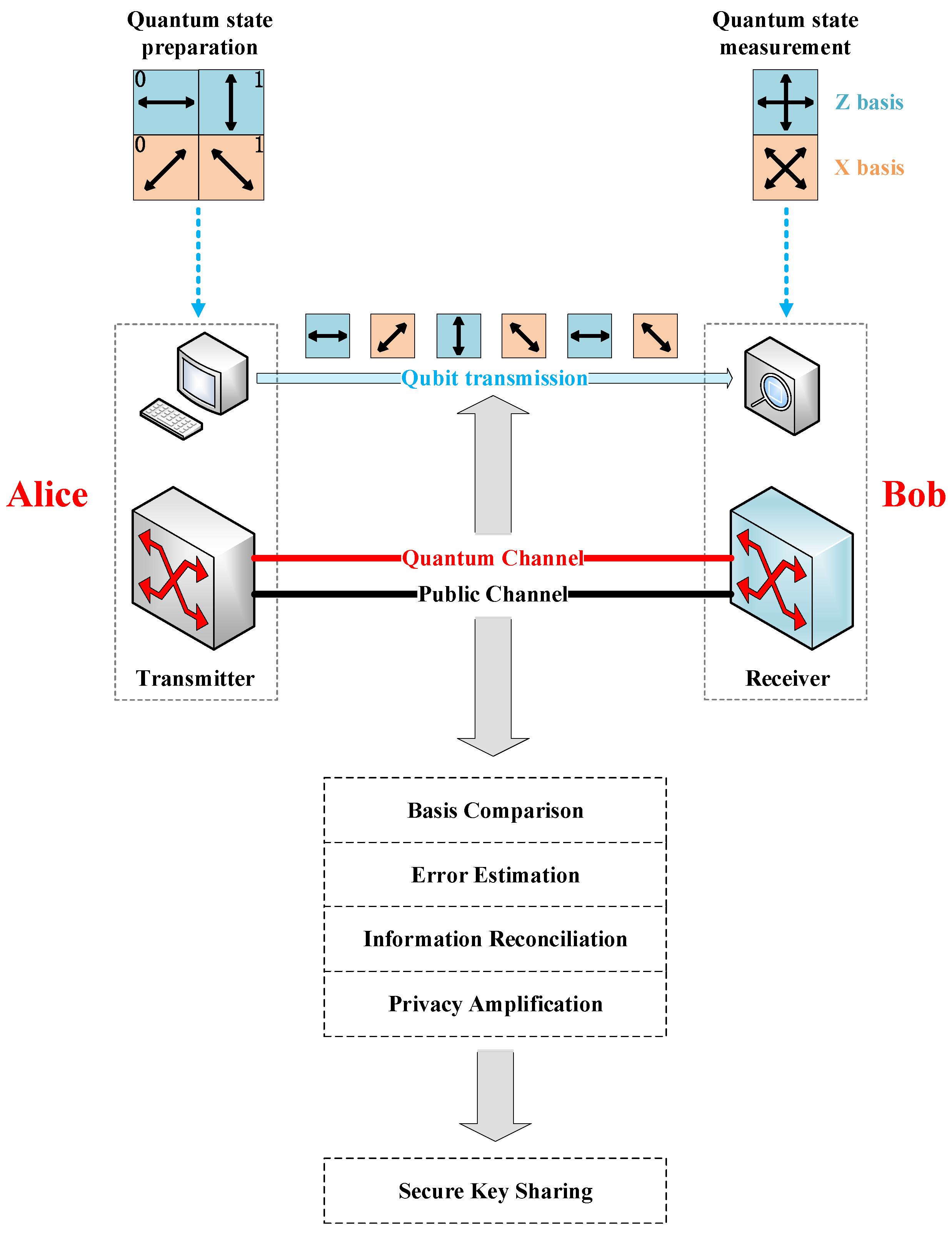
Entropy | Free Full-Text | A Resource-Adaptive Routing Scheme with Wavelength Conflicts in Quantum Key Distribution Optical Networks

Matteo Sordello, Zhiqi Bu, Jinshuo Dong · Privacy Amplification via Iteration for Shuffled and Online PNSGD · SlidesLive
High-Speed Implementation of Length-Compatible Privacy Amplification in Continuous-Variable Quantum Key Distribution
GitHub - rriemann/privacy-amplification: postprocessing for quantum cryptography raw data (master' thesis project)

Vitaly 🇺🇦 Feldman on X: "IMO the most significant recent development in privacy preserving data analysis are systems and models that use an anonymizing shuffler. However their formal analysis was rather involved

The procedure of accelerating length-compatible privacy amplification... | Download Scientific Diagram